The importance of data security cannot be overstated. With sensitive information being stored and shared online, it is crucial to ensure that documents are protected from unauthorized access and use. One of the most popular methods for sharing documents online is through secure data rooms and other online document sharing platforms. However, these platforms have been criticized for providing weak document protection. Here we explore the reasons why secure data rooms and other online document sharing platforms provide weak document protection.
Weak Document Protection
One of the main reasons why secure data rooms and other online document sharing platforms provide weak document protection is due to the complexity of data security. With the vast amount of data being stored and shared online, it can be difficult to ensure that all documents are properly protected. This complexity is further compounded by the fact that data security is constantly evolving, with new threats and vulnerabilities emerging on a regular basis. As a result, it can be challenging for online document sharing platforms to keep up with the latest security measures and ensure that all documents are adequately protected.
Lack of standardization
Another reason why secure data rooms and other online document sharing platforms provide weak document protection is due to the lack of standardization in data security protocols. With so many different platforms and tools available for sharing documents online, there is no standard set of security protocols that all platforms must adhere to. This lack of standardization can lead to inconsistencies in security measures across different platforms, making it difficult to ensure that all documents are equally protected. Furthermore, because different organizations have different security needs and requirements, there is no one-size-fits-all solution for document protection. Some organizations may require more stringent security measures than others, depending on the type and sensitivity of the information being shared. This means that document protection must be customized to meet the specific needs of each organization.
Possibility of Human Error
The possibility of human error presents another difficulty with online document sharing. Even with the most secure platform and protocols in place, human error can still lead to data breaches and leaks. For example, employees may accidentally share confidential information with the wrong person or fail to properly secure a document before sharing it online. While secure data rooms and online document sharing platforms can be useful tools for collaboration and information sharing, it is important to recognize their limitations and take steps to mitigate the risks associated with sharing sensitive documents online. This may include implementing strict security protocols, providing employee training on data protection, and regularly monitoring and auditing document access and usage.
Additionally, the design of some online document sharing platforms can also contribute to weak document protection. For example, some platforms may prioritize ease of use and convenience over security, leading to vulnerabilities that can be exploited by hackers. Furthermore, some platforms may rely on outdated or insecure encryption methods, making it easier for unauthorized users to access and view sensitive documents.
The human element is another feature that may lead to insufficient document security on online document sharing systems. Even while many platforms have strong security features, these only work when users stick to established practices for data security. Unfortunately, a lot of users might not understand how important data security is or might not take the appropriate precautions to make sure that their documents are adequately secured. For instance, users may use weak passwords or neglect to properly protect their devices, making it simpler for hackers to access private information. In addition, some users may also engage in risky behavior, such as sharing login credentials or downloading documents onto unsecured devices, which can further compromise document security. This highlights the importance of user education and awareness when it comes to data security. Organizations should provide training and resources to help users understand the risks associated with online document sharing and how to properly protect their documents. This may include guidelines for password creation, device security, and document access control. Moreover, it is important to regularly monitor and audit document access and usage to identify any potential security breaches. This can help organizations quickly respond to any security incidents and take steps to prevent similar incidents in the future.
Potential risks and take steps to mitigate
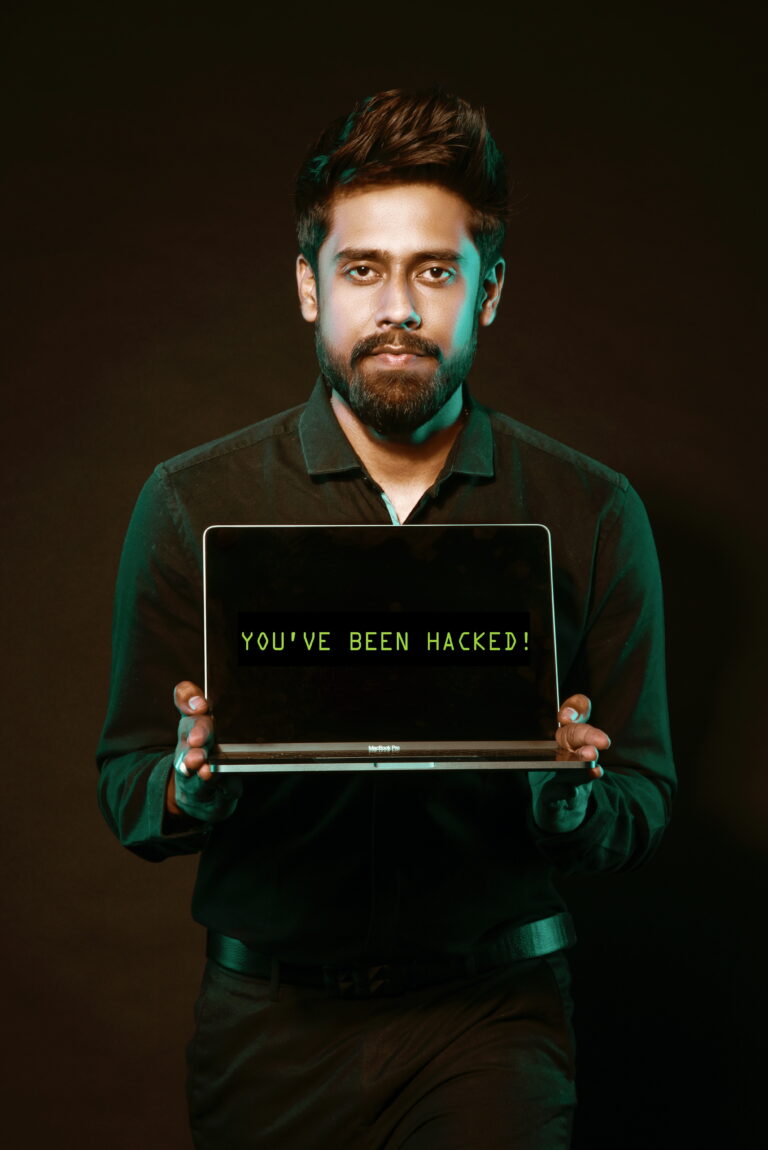
Overall, while online document sharing platforms can be a convenient and efficient way to collaborate and share information, it is important to recognize the potential risks and take steps to mitigate them. By implementing strong security protocols, providing user education and awareness, and regularly monitoring document access and usage, organizations can better protect their sensitive information and prevent data breaches. Finally, the rise of cybercrime has further exacerbated the problem of weak document protection on online document sharing platforms.
With hackers becoming increasingly sophisticated in their methods, it can be difficult for even the most secure platforms to keep up with the latest threats and vulnerabilities. Hackers may use a variety of tactics, such as link phishing scams and malware, to gain access to sensitive documents.
Once they have access, they may use the information for nefarious purposes, such as identity theft or corporate espionage. To combat this, organizations must stay vigilant and up-to-date on the latest security threats and vulnerabilities. They should regularly update their security protocols and invest in the latest security technologies to protect their sensitive information.
Importance of advanced security measures
Additionally, organizations should consider implementing multi-factor authentication and other advanced security measures to further enhance document protection. Ultimately, it’s crucial for businesses to have a strategy in place for handling a security breach or data leak. This may include assigning a staff to handle security incidents, contacting those affected, and taking precautions to avoid recurring problems. Organizations should also perform routine security audits to find any possible vulnerabilities and fix them. The effectiveness and currentness of the security measures in place can be helped by doing this. Businesses can reduce the dangers connected with online document sharing and guarantee the security of their sensitive data by taking these proactive measures. The organization is ultimately in charge of document protection, and it is up to them to take the required precautions to protect their data and avoid data breaches.
Conclusion
While secure data rooms and other online document sharing platforms offer many benefits, they also come with inherent risks. Weak document protection can result from a variety of factors, including the complexity of data security, the lack of standardization in security protocols, the design of the platform itself, human error, and the rise of cybercrime. To ensure that documents are adequately protected, it is important for both platform providers and users to take data security seriously. This includes following best practices for data security, such as using strong passwords, keeping software up-to-date, and avoiding suspicious links and emails.
Additionally, platform providers must continue to innovate and improve their security measures to keep up with the ever-evolving threat landscape. By working together, businesses can ensure that sensitive documents are protected and that online document sharing remains a safe and efficient way to share information. Likewise, it’s critical for businesses to thoroughly consider and choose a document sharing platform that satisfies their unique security demands and specifications. This can entail carefully examining the platform’s security policies and features as well as its history of data protection. In order to keep them current and useful, businesses should routinely examine their document sharing procedures and policies. In the end, safeguarding sensitive documents necessitates a thorough and multifaceted strategy that incorporates both technological and human components. Organizations can ensure that sensitive data is safeguarded and that they continue to gain from the many benefits of online collaboration and information by adopting a proactive approach to data security and cooperating with users to enable secure online document sharing.











+ There are no comments
Add yours